前兩年瘋狂的學 layout 和單晶片,做了幾樣東西出來。最近也蠻缺題材的,就把它寫下來吧。現在回顧一下,才發覺忘的有點乾淨!?不寫下來還真的不行啊,不然過兩年有突然燃起熱情,又要重頭來過了。
今天要先寫的是命令為 SecureEther 的有線網路,定時斷線裝制。原本是命名很炫的叫「Hacker Nightmare」,不過太嬉皮了,還是中規中矩一點好了。
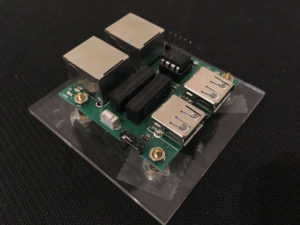
SecureEther 有線網路定時斷線器 – 功能介紹
這個裝置的行為,就是每兩個小時,會把有線網路中斷。目的是防止駭客在你人不在(ex. 下班)的時候偷偷操控、入侵你的電腦。也許有人會說寫個程式就好了,話也是沒說錯。但這個裝置的優點就是沒有OS平台的問題,也可以應用在其它場景,例如限制小孩使用網路的使用時

原本帥帥的產品名稱 – Hacker Nightmare
間。
它的原理是利用 PIC12F629 去控制兩個 RELAY,來斷開2個Ethernet Port (IN & OUT) 的 BID3+和 BID3- 。透過斷開這兩個 PIN, Windows 就可以偵測到網路線拔出,而顯示斷開的狀態。其實沒很瞭解 Ethernet PIN definition, 斷這兩個PIN是試出來的。
定時的功能,則是利用 PUSH Button 來驅動這個行為,按下時產生GPIO中斷。然後 PIC 就亮LED、連通Ethernet PINS,開始倒數一小時。然後斷線前五分鐘,會開始閃礫燈號。如果要繼續連線,就再按一下 PUSH Button,延長到一小時。
電路圖說明
功能簡單,也沒太複雜的電路。簡單的說明一下,文末會附上 EagleDesign 的原始檔。本來想附上淘寶的購買連結,不過很多都已經下架了,就只好附上購買的快照了,有需要的再買一樣型號。
- 左上角沒有Part-Number的那兩個正方型是 Relay,一個Relay用來控制一個 PIN 的連通與否,開關是透過 PIC 的 PIN7。
- RJ45-8LCT21-S: 就RJ-45的母頭
- PN87520-S: TYPE-A USB 母頭。主要是拿來供電的,會用兩個是想說不要佔用電腦一個USB Port,把隨身碟插在板子上,也可以被電腦
偵側到。但實際上USB是高速裝置,訊號線匹配有講究,所以最後只用到電的部份。
- PWR(MSK-12D19(1P2T)) : 拿來接一個1P2T Switch,當電源開關用的。
- J1: 線上燒錄器預留的腳。沒做好,記得是也不能燒…
- LED1: 狀態指示燈, 用 PIN5 控制。
- SW2: 輕觸開關,用來啟動網路連接。按下後會觸發PIC中斷,進行後續行為。
- R1: 這邊為什麼要特別提 R1呢?因為當按下SW2後, PIN6內部可能有電容會充電。當放開SW2後,要等很久電容的電被放光後,PIC才會偵側到狀態的改變。那時弄了很久,才想出這個道理。可能是簡單的單晶片才有這問題,以前那些跑Linux沒這現象。所以,我們加了這個R1,可以在SW2放開始,當做負載來放掉PIC PIN6相關電阻的電,然PIC可以快速偵側到改變。說白話一點,就是沒電阻會SW2放掉後幾秒內還是會讀到1,加了電阻就可以很快就讀到0了。
- PIC12F629_675: PIC 的8位單晶片,接腳少,符合需求應該是最大特點吧。1K Flash, 64b SRAM, 和 128 EEPROM.
PIC程式說明
程式部份的主要概念如下:
- 上電後燈閃礫三下,當做開機訊號
- 進入省電模式,如使用者此時按下按鈕,則會產生中斷喚醒PIC。
- 點燈,持續亮50分鐘。
- 最後10分鐘,則是亮2秒、暗兩秒。若此時再偵側到有按鈕,則將時間恢復到1小時。由於這邊的按鈕偵側是用POLLING的,有可能會沒偵測到,所以要稍微按久一點。
- 60分鐘到後,關燈,進省電模式。接著就到步驟(2),一直跑下去。
程式碼

PIC12F675 PIN Defintion
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 |
/* Header 省略 */ void interrupt ISR() { GPIF=0; //清除狀態, 不然中斷會持續發生 } void main() { int remain_timer = 0;//倒數1小時的秒數counter int t; int wakeup=0; //設定 GPIO 方向, GP3,4,5沒用到 //GP0=OUPUT, 控制 Relay //GP1=INPUT, 接到 SW2 //GP2=OUTPUT, 接到 LED TRISIO = 0b111010; ADCON0=0b111; //AD 功能打開, 但ANSEL實際都設成0, 所以都做為數位用途 ANSEL=0; CMCON=7; //單晶片有 Analog Comparator 的功能,設成7關閉 GPIO=4; //一次設定所有的GPIO值,BIT2=1 就是 GPIO2 輸出, 點 LED 燈 __delay_ms(1000); GPIO=0; //GPIO全設成0, 關LED. 就是上電時,燈量一秒然後暗掉,當提示燈 GIE=0; //先關閉中斷 GPIE=1; //設定 GPIO 狀態改變會產生中斷 IOC1=1; //設定 GPIO1 狀態改變時會產生中斷 /* IOC0~5: 是設定per pin(在GPIE=1狀況下)是否產生中斷 */ while (1) { if(remain_timer == 0) { //如果秒數倒數到0了,就進省電模式 //把所有GPIO輸出關掉,並且讀取一次,以確保前次的輸入狀態被清掉 GPIO=0; __delay_ms(100); t=GPIO; GPIF=0;//讀取GPIF,清除前次的中斷狀態,以免一睡就醒 GIE=1; //開始中斷 SLEEP(); //進省電模式 GIE=0; //運作中,不需中斷了,關閉中斷 //從省電模式醒來後,設定一個flag. 原本是要用GPIO1的值來判斷, 但似忽有時會讀到0。 //也許是SW2放開太快 wakeup = 1; } if(GP1 || wakeup) { //是醒過來的,或偵測到GPIO1有值(SW2被按下) wakeup = 0; __delay_ms(100); remain_timer = HOUR_1; //把倒數再設成1小時 GPIO=5; //5=BIT0 + BIT2, 開啟網路,和點燈 } //最後5分鐘閃燈 if((remain_timer > 0) && (remain_timer < MIN_5)) { if(remain_timer & 1) GPIO=5; //開啟網路+點燈 else GPIO=1; //只開啟網路 } if (remain_timer > 0) remain_timer--; __delay_ms(1000); } } |
展示影片
介紹一下實品,還有實際的操作狀況。
SecureEther 算是被公司逼出來的無聊小玩具, 一直被駭, 只好定時把網路關掉…不過後來也沒再被駭了, 可能感受到我的決心 XD
附件
- PIC12F675 Datasheet – 太大了, 請各位自己抓, 網路上都有
- SecureEther2.X MPLabX 原始碼
- SecureEther EagleDesign 電路圖/PCB